Phishing is a crime employing both social engineering and technical subterfuge to steal consumers' personal identity data and financial account credentials. Social engineering schemes prey on unwary victims by fooling them into believing they are dealing with a trusted, legitimate party, such as by using deceptive email addresses and email messages. These are designed to lead consumers to counterfeit websites that trick recipients into divulging financial data such as usernames and passwords. Phishing messages can also contain malicious attachments, opening them will execute malware and infect the victim's device. Email content can specifically target a group of people sharing some common elements (e.g., workplace, shopping at the same store..), and can be customized by the attackers towards this goal. This more refined variant of phishing is called spearphishing.
To promote phishing awareness, we designed an educational campaign targeting people at the University of Padova: students, professors and technical-administrative staff members. To increase the effectiveness of our initiative, we sent fake phishing emails to anonymized Unipd email accounts and redirected all the victims to an educational landing page.
We designed different email templates according to the targeted threat: previous phishing attempts sent to UniPD, generic phishing attempts, and spearphishing attempts. We delivered three batches of phishing emails (March, May and June 2020) to 1.508 people (4.524 emails in total), and monitored the reaction (i.e., how many participants clicked the malicious link embedded in the phishing email). The results of our phishing assessment campaign will be made public after the acceptance of the paper.
To design the email templates, we identified five different threatening scenarios: previous phishing attempts delivered to UniPD (i.e., Scenario 1), generic phishing attempts (i.e., Scenario 2), spearphishing attempts targeting students (i.e., Scenario 3), spearphishing attempts targeting professors (i.e., Scenario 4) and spearphishing attempts targeting technical-administrative staff members (i.e., Scenario 5). Below, we provide examples of each scenario.
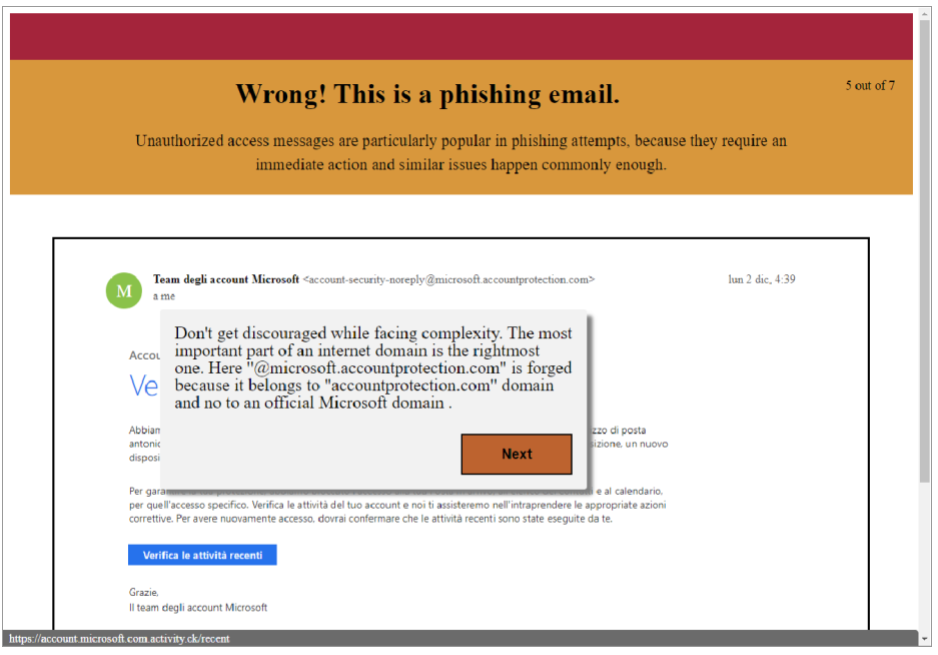
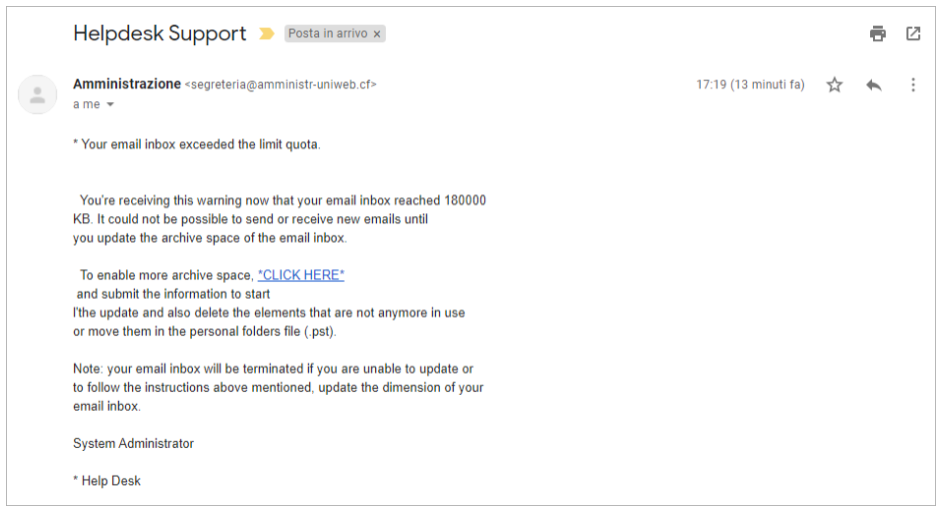
Scenario 1 - The user receives a warning concerning the maximum storage limit of his email account, and is encouraged to request more space by visiting a malicious link (see Fig. 1).
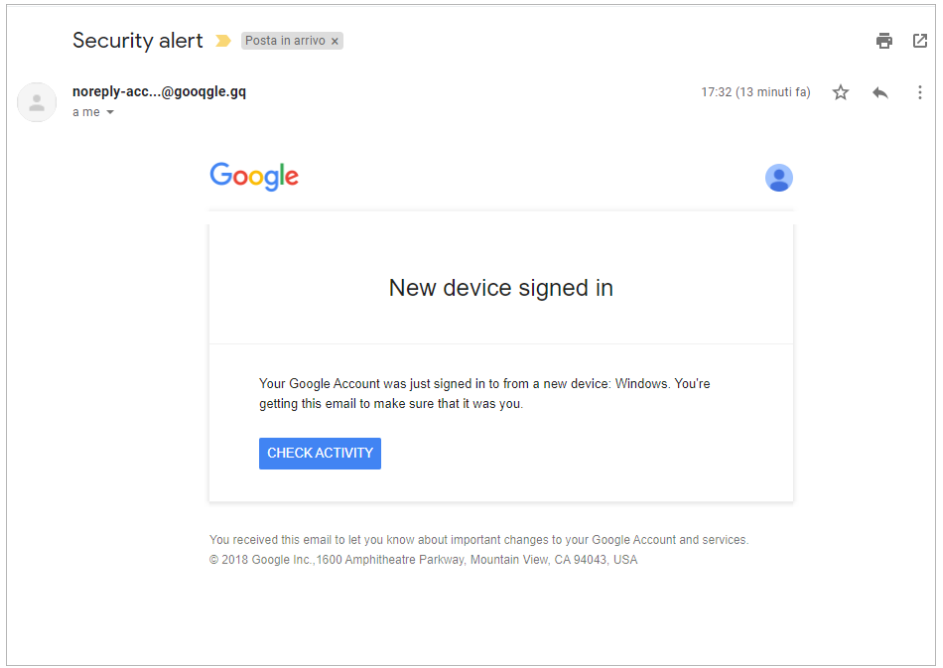
Scenario 2 - The user receives a warning about a new unknown device signing into his Google account, and is encouraged to check the account activity by visiting a malicious link (see Fig. 2).
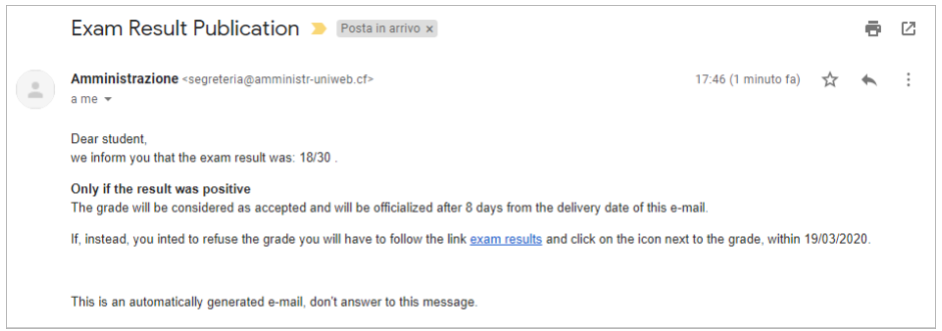
Scenario 3 - The student is notified about a new grade equal to 18/30. Being aware that the grade is automatically accepted if not otherwise specified, the student is lured to visit the malicious link (see Fig. 3).
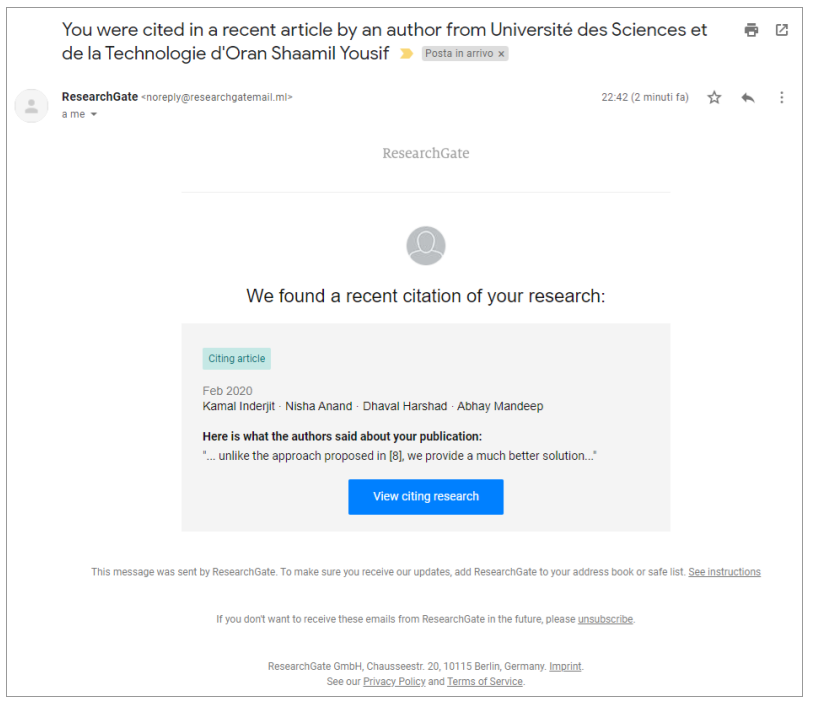
Scenario 4 - The professor is notified about a new citation of one of his published works and he is attracted to visit the malicious link (see Fig. 4).
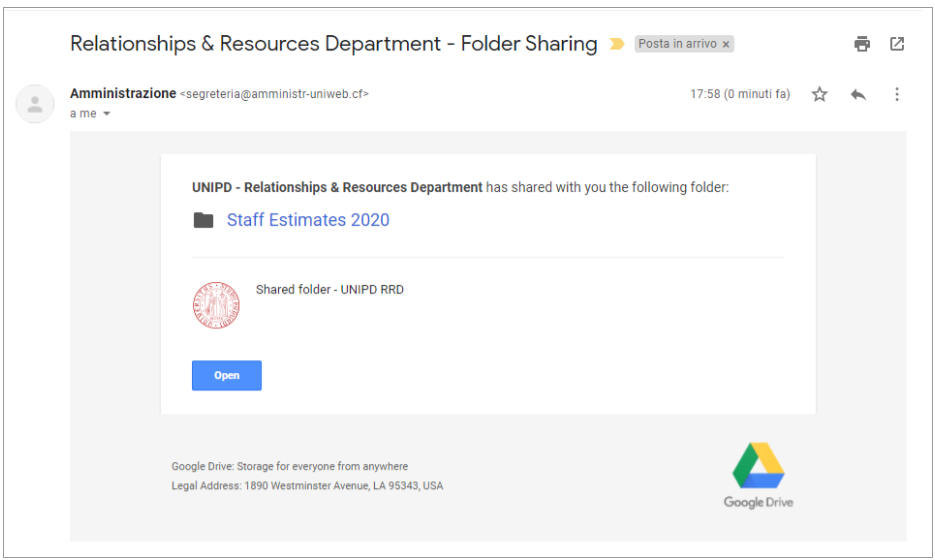
Scenario 5 - The technical and administrative staff member receives an unexpected file which might contain confidential financial data. The sense of curiosity pushes the victim into visiting the malicious link (see Fig. 5).
You can watch it on the video player below.
You can challenge your knowledge about phishing with our quiz (Italian language only) by visiting https://quiz-unipd-phishing.herokuapp.com, and compare your results with other anonymous participants. Below, we show a screenshot of the quiz.